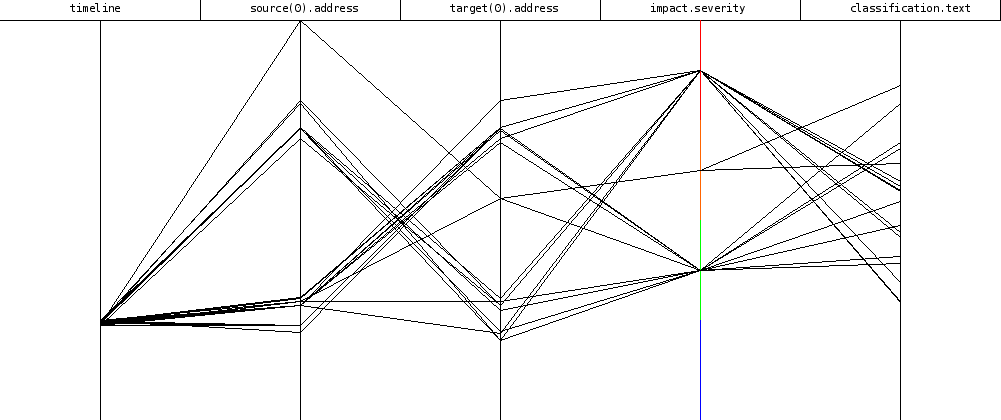
Captive portals almost always work by validating the IP address of the client, and often the MAC address. This creates a wrong feeling of security, because it is quite easy to bypass. Let’s explain the most common problem: spoofing.
Installing a captive portal
I have chosen to install Alcasar, which claims to be a highly secure solution developed by the French Ministry of Defense.
First surprise, it’s a shell script ! In fact, it’s not really an application, only an installer for a few packages, with some configuration. Installation went pretty bad:
- the installer only works for a specific version of Mandriva (2007), which is quite old, and buggy on my hardware
- most things are hardcoded: the installer exploded without errors because my network is not ending by a 0 (10.0.0.129/25)
- my third network card is not even used by the script ! Too bad for the DMZ
After 4 or 5 retries, and modifications in the script, I finally got a working server.
First tests
After a reboot, everything seems to work. Got an address using DHCP, I try to connect to Google .. ok, the captive portal appears and asks for a login. With …
read more